DCSync
DCSync is a credential dumping technique that can lead to the compromise of individual user credentials, and more seriously as a prelude to the creation of a Golden Ticket, as DCSync can be used to compromise the krbtgt account’s password.
To perform a DCSync attack, an adversary must have compromised a user with the Replicating Directory Changes All and Replicating Directory Changes privileges. Members of the Administrators, Domain Admins, Enterprise Admins, and Domain Controllers groups have these privileges by default. It is also possible for any user to be granted these specific privileges. Once obtained, an adversary uses the Directory Replication Service (DRS) Remote Protocol to replicate data (including credentials) from Active Directory.
In addition to domain controllers, some applications – such as Azure Active Directory Connect – have legitimate requirements for replication permissions, but can also become targets for adversaries because of them.
Threat Summary
Target:
Active Directory
Tools:
ATT&CK® Tactic:
ATT&CK Technique:
Difficulty
Detect:
Hard
Mitigate:
Medium
Respond:
Variable
How DCSync Works
Hover to see each step
Detect, Mitigate, and Respond
Difficulty: Hard
It is possible to detect a DCSync attack by monitoring network traffic to every domain controller, or by analyzing Windows event logs.
Network monitoring
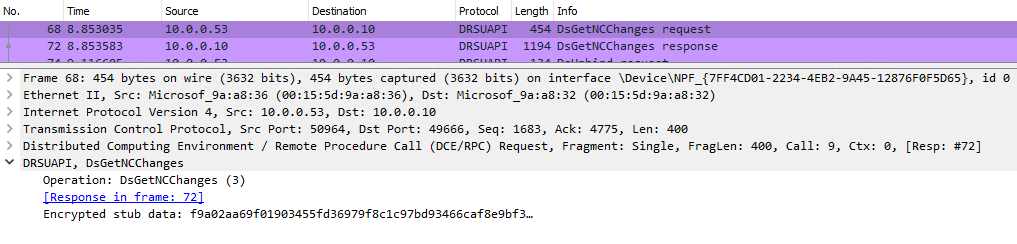
Monitor network traffic for DRSUAPI RPC requests for the operation DsGetNCChanges and compare the source host against a list of domain controllers. If the source host does not appear on that list, then a DCSync attack is suspected. However, without significant investment in packet analysis it is not possible to determine which objects were replicated.
Windows event logs
Event ID 4662 in the subcategory Audit Directory Service Access audits basic information about users performing operations within Active Directory for events specified in an object’s system access-control list (SACL).
Using this event, it is possible to see when a user exercises their Replicating Directory Changes All extended right by filtering the properties field to include {1131f6ad-9c07-11d1-f79f-00c04fc2dcd2} which is the control access rights GUID for replicating directory changes.
However, Active Directory event logs only reveal which objects were replicated when diagnostic logging is enabled. Diagnostic logging can have performance impact and is not likely suitable for long-term production use.
Difficulty: Hard
Replication amongst Active Directory domain controllers is a normal part of their operation. Mitigating the risk of DCSync involves protecting replication permissions from abuse.
- Routinely audit replication permission grants and aggressively embrace the principal of least privilege
- If a legitimate need for replication permissions exists, adopt compensating controls to mitigate the risk of credential theft
- Alert, in real-time, on changes to replication permissions
- Do not allow users to possess administrative privileges across security boundaries. This greatly reduces the risk that an adversary can escalate their privileges.
Difficulty: Medium
Should the use of DCSync be detected, there are several actions one can take to immediately respond. The actions and response difficulty depend upon what was replicated. If only non-privileged users were replicated, then the response difficulty is moderate; if the entire domain or krbtgt was replicated, the response is extremely hard.
- Activate the incident response process and alert the response team
- Reset the password of the user that performed the unauthorized DCSync and optionally disable the user to a) force instantaneous replication to all domain controllers, and b) disrupt the adversary’s use of that account
- Quarantine the impacted machines for forensic investigation, as well as eradication and recovery activities
- Determine which account’s credentials were replicated:
- If only specific users were replicated, reset the passwords for those users
- If the entire domain or the
krbtgtuser was replicated, you should activate your incident response plan for total Active Directory compromise which should include, but not be limited to, a password reset (twice) of thekrbtgtuser.